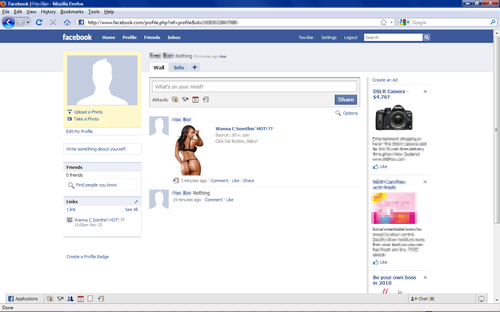
Facebook Hit With A New Clickjacking Worm
The attack began when a victim encountered the image of the near-naked woman on a friend’s profile page along with the words “Want 2 C something hot? Click da button, baby!” Facebookers who took the bait – and were logged in to their accounts at the time – found their profile pages were updated to include the same image. The more people who fell for the come-on, the more the come-on was presented to new potential victims, giving the attack a viral quality.
Researchers who first spotted the ruse attributed it to a CSRF, or cross-site request forgery, vulnerability on Facebook’s site. A spokesman for the social networking site disputed that explanation, saying the attack was really the result of clickjacking.
“This problem isn’t specific to Facebook, but we’re always working to improve our systems and are building additional protections against this type of behavior,” Facebook spokesman Simon Axten wrote in an email. “We’ve blocked the URL associated with this site, and we’re cleaning up the relatively few cases where it was posted (something email providers, for example, can’t do).”
Clickjacking is a vulnerability at the core of the web that allows webmasters to trick users into clicking on a link they didn’t intend to. The exploits are pulled off by superimposing an invisible iframe over a button or link. Virtually every website and browser is susceptible to the technique. Websites that accept user-generated content make especially potent launch pads for such attacks.
This latest attack is a reminder that it’s often impossible to know where a given link will lead, even for careful users. Indeed, Gadi Evron, one of the security researchers who first spotted the exploit, confessed to having his Facebook page briefly display the image after first encountering it on a friend’s page.
“This shows that even experts can become complacent and trust systems when they really shouldn’t,” he wrote.
Facebook administrators have already blocked the clickjacking exploit.
Credit: The Register, AVG Blogs
More on CyberInsecure:












 Posts
Posts





Leave a Reply
Comments with unsolicited links to other resources will be marked as spam. DO NOT leave links in comments. Please leave your real email, it wont be published.