Infecting Christmas E-greetings Are Distributed Via Spam
Websense Security Labs has discovered that malware authors are already using Christmas themes this year as a social engineering tactic, in an effort to gain control over compromised machines. This campaign uses email messages in the form of e-greetings, leading to supposed animated postcards. These actually lead to a Trojan backdoor that has been distributed in previous malicious spam campaigns.
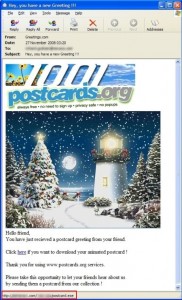
The email messages, spoofed to appear as though they have been sent from postcards.org, display an animated Christmas scene. A URL link within the email leads to a malicious file called postcard.exe hosted on various servers, including those in the .com domain space.
Once executed, a backdoor is created by the malware author enabling access and control over the resources of the compromised machine. Control is conducted over IRC, communicating with ircserver.*snip*.la. During the install process an image called xmas.jpg is displayed to the user as a distraction technique.
Example of malicious email:
More on CyberInsecure:











 Posts
Posts





November 28th, 2008 at 2:09 am
redirecting technique is too familiar for spam , i dont like it , cheating !! simple wthot tech knowledge !