Koobface Worm Creates A Low-cost, Distributed CAPTCHA Breaking Service
A new Koobface spam campaign which involves Youtube copycat web page eventually leads users to CAPTCHA solving. This time, instead of using cheap labor, Koobface is using the infected users themselves to break CAPTCHAs.
The scheme uses the old flash player trick where the user is told that they need to download the latest version of Adobe Flash Player to view a certain video. In this case, the Flash Player in the page is an actual Flash .SWF file, which will redirect users to a file named setup.exe detected by Trend Micro as TROJ_KOOBFACE.DU through the Smart Protection Network.
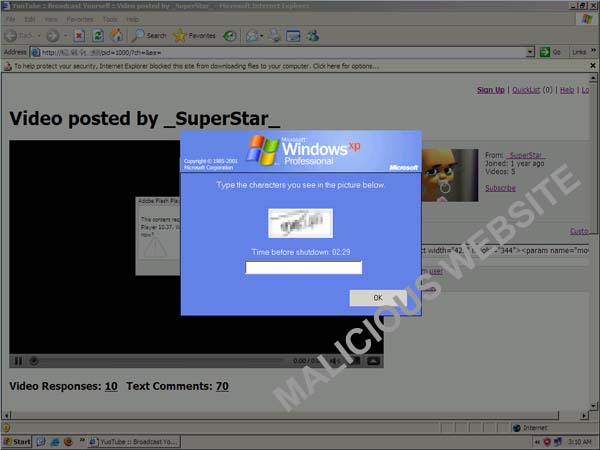
A short while after running setup.exe, Koobface fetches a picture file from a remote server which is actually a CAPTCHA image. The user is then presented with the Windows prompt.
The panic-inducing screen displays the time before the system will shutdown while the image (blurred) in the middle is the downloaded CAPTCHA image. The above prompt is essentially telling the user that the system will shutdown in 2 minutes and 29 seconds unless they enter the CAPTCHA correctly!
After the user correctly solved the CAPTCHA image, Koobface promptly reports the solved CAPTCHA code to a remote server. This Koobface strategy creates a low-cost, distributed CAPTCHA breaking service.
Credit: TrendLabs, TrendMicro Blog
More on CyberInsecure:











 Posts
Posts





Leave a Reply
Comments with unsolicited links to other resources will be marked as spam. DO NOT leave links in comments. Please leave your real email, it wont be published.