Multiple MPAA and RIAA Websites XSS Vulnerability Allows Rogue Content
Cross-site scripting flaw on the web sites of the Motion Picture Association of America (MPAA) has been abused to inject listings from controversial torrent links site The Pirate Bay.
Vektor, a member of the Team Elite group of hackers, smuggled links culled from the The Pirate Bay into content served up when surfers visited the MPAA’s recommended list of sites. The MPAA’s legal action against The Pirate makes the supposed endorsement ironic and embarrassing, if not completely unexpected.
Cross-site scripting (XSS) security flaws on websites are all too commonplace and the MPAA is a high-profile target, especially after the four defendants in The Pirate Bay trial were found guilty in a recent high-profile trial. So it was only really a question of time until hackers managed to find a chink in its armor to exploit.
Earlier denial of service attacks against entertainment industry websites scored limited successes in the aftermath of The Pirate Bay verdict on 17 April.
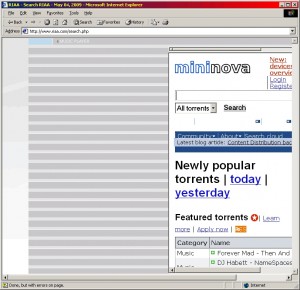
According to Vektor, the Recording Industry Association of America (RIAA) website is vulnerable to similar flaws as those he exploited to embarrass the MPAA earlier this week, Softpedia reports. Vektor used this flaw to inject a listings from Mininova, another well known torrent tracker, into pop-up windows displayed when users visited portions of the RIAA website.
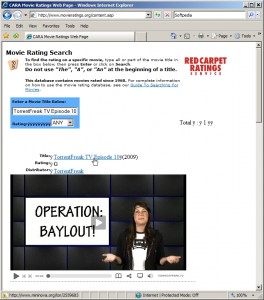
Although the MPAA has reportedly addressed the flaws on its main website following the attack, other MPAA-controlled websites involved in movie ratings remain vulnerable to much the same type of exploit.
The vulnerabilities create a means for rogue iFrames from third-party servers to be presented to surfers as if they came from the site they are visiting, when in reality they come from locations determined by hackers.
XSS flaws on both the MPAA and RIAA websites have cropped up from time to time in the past, a quick search of security website XSSed reveals. Security suppliers, such as application security firm Fortify, said that Vector’s attacks against the RIAA and MPAA were each effectively accidents waiting to happen.
“That such sites are open to XSS-driven incursions and alterations comes as no surprise, given the fact that so many sites are poorly programmed and therefore open to such attacks,” said Richard Kirk, a director at Fortify. “The MPAA is lucky that Vektor’s attack was a proof-of-concept one, and intended as something of a joke. The next time they – and other organizations whose sites are vulnerable to XSS-driven attacks, may not be so lucky,” he added.
Credit: The Register
Credit: Softpedia
More on CyberInsecure:











 Posts
Posts





Leave a Reply
Comments with unsolicited links to other resources will be marked as spam. DO NOT leave links in comments. Please leave your real email, it wont be published.