Google Flooded With More Than A Million Of Open Redirect Links That Infect Users With Malware
According to researchers from CyberCrime & Doing Time blog, a Google search showed that the web is littered with more than one million links pointing to a single rogue domain. While the links appear to point to trusted domains, people who click on them are taken to a malicious website that claims they need to install security software or offers to stream video.
Miscreants are exploiting weaknesses in webpages operated by the federal government, media companies, and even Microsoft to trick unwitting visitors into installing harmful software that takes over their computers. Sites like Microsoft.com, IRS.gov, countless media outlets, magazines, universities, and other websites can be found in the search engines in this way.
The scam takes advantage of websites which have a “URL redirect” on them. A URL redirection program allows the website owner to “send” users to another website, while keeping track of where they went. They are often used in conjunction with an exit page that says something like “You are now leaving our site and being redirected to a new location.” The problem is that many of those sites actually allow other people to use their URL to redirect traffic as well. The miscreants have managed to cause Google to “learn” many of these URLs by placing them on sites they control.
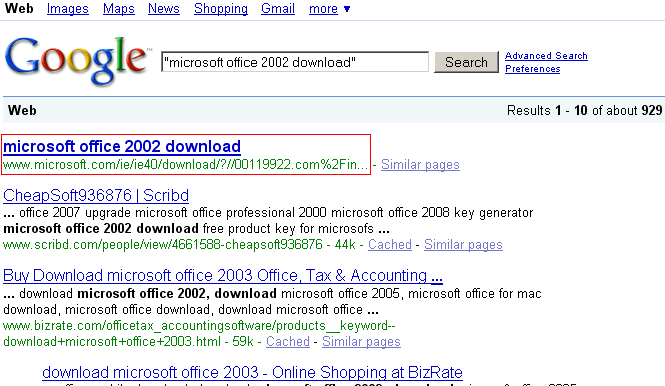
Currently the redirections are injected for the domain 00119922.com, which was registered December 19th to infect users. An example search terms results the Microsoft open redirector as the number one search result on Google:
Some of the other sites with open redirectors being targeted by attackers include: dbrecovery.com, togshop.com, wnbc.com, mrm.mms.gov, countrycurtains.com, portugal-info.net, cyberswim.com, nbcsandiego.com, thebostonchannel.com, thepittsburghchannel.com, hermanstreet.com, viadeo.com, nationalgeographic.com, barronscatalog.com, click2houston.com, lucy.com, wgal.com, rexart.com, kitv.com, bookmatestore.com, attarbazaar.com, titlenine.com, vermontteddybear.com, readthehook.com, theessentials.com, martlmadidebeli-gristianoba.com
The attacks can be especially useful in tricking users to install software. Many of the Microsoft links, for example, appear to relate to an Internet Explorer download, so users are already prepared to install software on their machines. However, the Microsoft links redirect users to a site that runs a fake computer scan that purports to find dangerous malware, then offers a rogue “anti-virus program” for users to run.
Other exploited websites offer video streaming, so visitors may not be surprised when they’re told they need to install a new codec – and that’s exactly what happens.
The perpetrators of this scam have planted comments all over the web that cause search queries such as “download fruityloops 6 free” (and many relating to porn) to return high-ranking results that point to popular sites that are vulnerable to the exploit.
More on CyberInsecure:











 Posts
Posts





July 27th, 2010 at 8:18 am
IT People in general looked down on the web application threats. Now, we’re seeing more and more dangerous mass attacks using web exploits. Well done. They are starting to be afraid that web threats are more than an XSS alert box.